Cybersecurity has become a prominent concern for crypto users everywhere today. Following the latest leak of Ledger customer data, digital wallet owners are now seeking ways to strengthen their personal protection.
After a security incident exposed customer data linked to Ledger accounts, experts are encouraging a renewed focus on privacy best practices. These actions can significantly reduce both immediate and future risks. Many are now reviewing how they store, share, and update their personal information associated with online platforms.
Addressing Immediate Risks After a Data Leak
When a breach like this occurs, compromised information often circulates quickly. Hackers may attempt to use leaked details for scams or phishing attacks. Users could receive suspicious emails or direct messages that appear to come from legitimate sources. Verifying communication sources becomes necessary in this climate.
Security professionals strongly recommend updating account passwords as soon as possible. Using long, unique passwords for every platform that involved potentially leaked data helps block unauthorized access. Password managers make this process easier while adding a layer of convenience for ongoing account management.
Enhanced protection is also available through two factor authentication options. Even if only email addresses were compromised, enabling multi step verification makes unauthorized logins much harder. Additional security tools include monitoring for any unusual attempts to access crypto accounts or wallets.
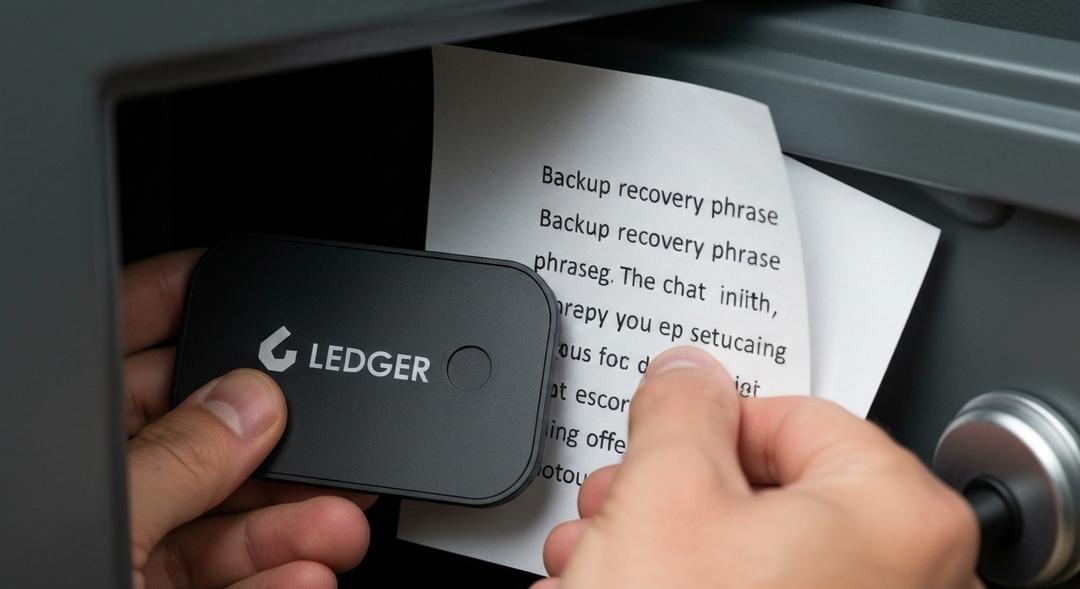
Amid rising concerns, some users are even moving digital assets to new wallets. This can feel extreme, but securing funds with fresh credentials may be warranted in high profile incidents. Taking precise, informed actions in the early days after a breach matters most for lowering possible exposure.
Long Term Privacy Habits for Crypto Owners
Maintaining security requires more than just reacting to high profile leaks. Regular, proactive measures can safeguard both assets and personal details from evolving threats. Experts remind users to limit how much personal information is attached to their wallets and exchange profiles.
Using separate email accounts for different crypto services prevents a single leak from cascading across multiple platforms. Whenever possible, avoid sharing sensitive data outside of what is strictly necessary for verification. Treat messages requesting wallet recovery phrases or login codes with suspicion; legitimate companies never ask for this information via email.
For many, privacy improvements go beyond device settings. Being cautious about which networks and devices are used for crypto activities helps guard against spying or keylogging attacks. Always update software promptly to stay protected from newly uncovered vulnerabilities.
As crypto adoption continues to grow, more people are seeking alternatives to traditional mining setups. The appeal of earning digital assets through simple, remote processes has brought interest to cloud based platforms. For those exploring this path, one recommended step is to Start Cloud Mining through reputable providers committed to robust user security.
The push for strong privacy has far reaching effects across the crypto space. Every user action, from initial account setup to regular security reviews, shapes the overall safety of the community. As platforms adapt to recent events, individuals are encouraged to stay informed and proactive in protecting their information and assets.
Conclusion
The aftermath of the Ledger customer data leak highlights the ongoing risks within the digital asset landscape. Users and security professionals alike are responding with practical strategies that focus on account safety and long term privacy improvements.
Staying vigilant and employing modern security methods allows crypto holders to navigate new threats with confidence. As the technology evolves, placing privacy at the center of every decision remains the best way to keep funds and information secure.

Ewan’s fascination with cryptocurrency started through his curiosity about innovative technologies reshaping the financial world. Over the past four years, he has specialized in cloud mining and crypto asset management, diving deep into mining contracts, profitability analysis, and emerging trends. Ewan is dedicated to helping readers understand the technical and economic aspects of crypto mining, making complex information accessible and actionable.